The brains behind Magicapk.com-- the website that apparently leaked user details of 120 million Reliance Jio subscribers on Sunday-- are yet to be identified. Meanwhile, the telco's claim that the data breach was "inauthentic" has been challenged by many Jio users, who said they had found their credentials on the website, before it was taken down by the hosting provider.
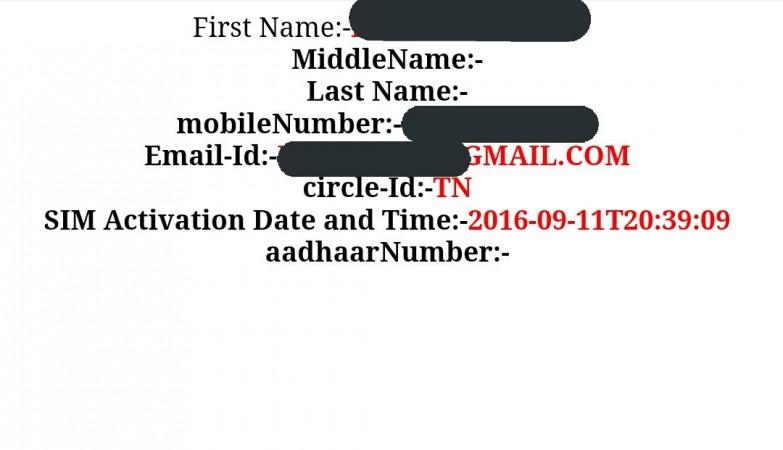
Many Reliance Jio users in India reported on Sunday night that Magicapk.com had access to sensitive customer details, including mobile numbers, email IDs, first name, last name, SIM activation date and the location from where the connection was activated. The data breach has likely affected all Reliance Jio users and the company currently has over 100 million subscribers.

"We have come across the unverified and unsubstantiated claims of the website and are investigating it. Prima facie, the data appears to be inauthentic. We want to assure our subscribers that their data is safe and maintained with highest security," Reliance Jio said in a statement.
Many people, however, took to Twitter and said Jio's claim was not true.
Jio's claim that the data in the leak appears unauthentic is bullshit. Multiple people, including me, have verified https://t.co/UlErjOtktf
— Nikhil Pahwa (@nixxin) July 10, 2017
This Reliance Jio user data leak is real. Just tested. https://t.co/JJcuadzm6Y
— Gaurav Singh (@sgaurav_baghel) July 9, 2017
Various reports also confirmed the data breach.
Magicapk.com
We've done a bit of digging to track down Magicapk.com. The research showed the website was registered in India. However, the people behind the website are still unknown.
Here's the details about Magicapk.com we've got from myip.ms, an online tool that offers a comprehensive report on any website or I.P. address, including the hosting provider, the physical location of the website, the IP Address history and the DNS information.
Some key information about Magicapk.com:
- Magicapk.com Registered on: 18 May 2017
- Magicapk.com Last Updated on: 18 May 2017
- Magicapk.com Expires on: 18 May 2018
- IP Address: 103.195.185.104
- IP Location: India
- IP Reverse DNS (Host): cp-in-10.webhostbox.net
- Hosting Company: P.d.r Solutions Fzc
- Website Nameservers: NS1.CP-IN-10.WEBHOSTBOX.NET / NS2.CP-IN-10.WEBHOSTBOX.NET
Though Magicapk.com is currently inaccessible, it doesn't necessarily mean the leak never happened, or the leaked data will not surface again.








