WhatsApp and Telegram are popular IM apps with a global user base and their popularity is in part for their utmost security with end-to-end encryption. But it looks like the very thing these apps boast of has a loophole that can be exploited by notorious hackers.
Cyber-security firm Symantec on Monday revealed vulnerabilities in WhatsApp and Telegram apps that could allow hackers to slyly manipulate media files, including images and audio files, stored on the phone's external storage. Owing to this practice, the researchers are calling the flaw "Media File Jacking" and it affects only Android versions of both apps.
"If the security flaw is exploited, a malicious attacker could misuse and manipulate sensitive information such as personal photos and videos, corporate documents, invoices, and voice memos," software engineer Alon Gat and Yair Amit, VP and CTO, Modern OS Security, Symantec, wrote in a blog post.
How does Media File Jacking work?
According to The Verge, WhatsApp and Telegram save files either in the internal or external storage of the device. The malware, if entered your Android smartphone, can access files saved in external storage to exploit data. The malware works in the background and can manipulate files even before the user has seen them. The researchers also noted that hackers could even alter an outgoing multimedia message.
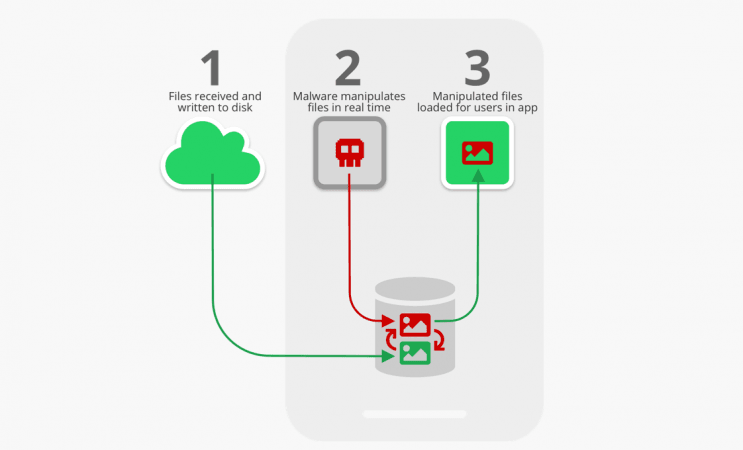
Listing out certain possibilities, researchers said that hackers could modify a photo before the recipient sees it, manipulate an invoice to trick a user into making payment to an illegitimate account, spoof audio messages or even spread fake news. All of this happens in the background in real-time without the user realizing anything.
"The Media File Jacking threat is especially concerning in light of the common perception that the new generation of IM (instant messaging) apps are immune to content manipulation and privacy risks, thanks to the utilisation of security mechanisms like end-to-end encryption," researchers noted.
How to be safe?
There are several practices in making sure a user is not fooled by such malware attacks. In the wake of this attack, users can ensure the files are stored internally. WhatsApp users can go to Settings > Chats > Media Visibility and turn off the setting. Similarly, Telegram users can go to Settings > Chat Settings > Save to Gallery and turn it off.

Users must also make sure they do not download apps from a third-party source, through which malware-ridden apps can easily bypass verifications otherwise done by Play Store.
Telegram hasn't issued a statement in this regard, but WhatsApp is working on a fix. "The suggested changes here could both create privacy complications for our users and limit how photos and files could be shared," WhatsApp spokesperson said in a statement.











!['Talks & Terror can't go hand-in-hand, India won't tolerate nuclear blackmail': PM Modi's ztern warning to Pakistan [Key takeaways from success of Operation Sindoor]](https://data1.ibtimes.co.in/en/full/816062/talks-terror-cant-go-hand-hand-india-wont-tolerate-nuclear-blackmail-pm-modis-ztern.jpg?w=220&h=138)




