
The upcoming Winter Olympics in South Korea is being targeted by hackers with a phishing and malware campaign, researchers at cybersecurity firm McAfee have discovered.
The researchers revealed in a blog post that the campaign has targeted organisations involved with the Pyeongchang Olympics scheduled to take place between February 9 and February 25.
According to them, the hackers have attached a malicious Microsoft Word document in an email which was primarily targeted at icehockey@pyeongchang2018.com, the email address associated with ice hockey at the Winter Olympics, with several organisations in South Korea copied on the BCC line.
"The majority of these organisations had some association with the Olympics, either in providing infrastructure or in a supporting role. The attackers appear to be casting a wide net with this campaign," the researchers said.
As part of the malware campaign, which began on December 22, the attackers originally embedded an implant into the malicious document as a hypertext application (HTA) file. Then they quickly moved it to hide it in an image on a remote server and used obfuscated Visual Basic macros to launch the decoder script.
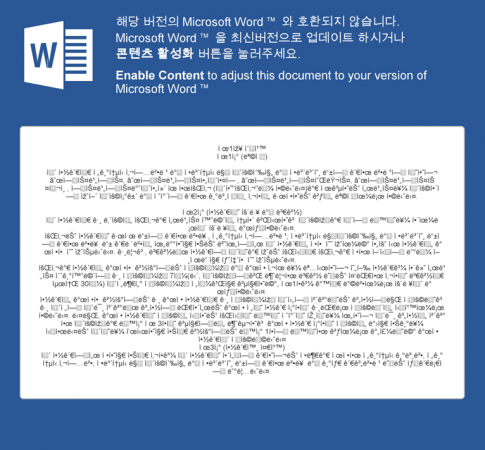
If opened, the document tells victims that they must click to enable content. If done accordingly, it allows the macros to install the malware to run a hidden PowerShell script embedded within the image file.
The researchers also found that the hackers used an open source stenography tool, released on December 20, to embed the PowerShell script into the image file, allowing them to hide malicious PowerShell code in a visible image on a remote server.
"The attacker's objective is to make analysis difficult and to evade detection technologies that rely on pattern matching. Because the obfuscation makes use of native functions in PowerShell, the script can run in an obfuscated state and work correctly," researchers said.
Further analysis also revealed that this implant establishes an encrypted channel to the attacker's server, likely allowing the attacker to execute commands on the victim's machine and to install additional malware.
"With the upcoming Olympics, we expect to see an increase in cyberattacks using Olympics-related themes. In similar past cases, the victims were targeted for their passwords and financial information," the researchers said.














