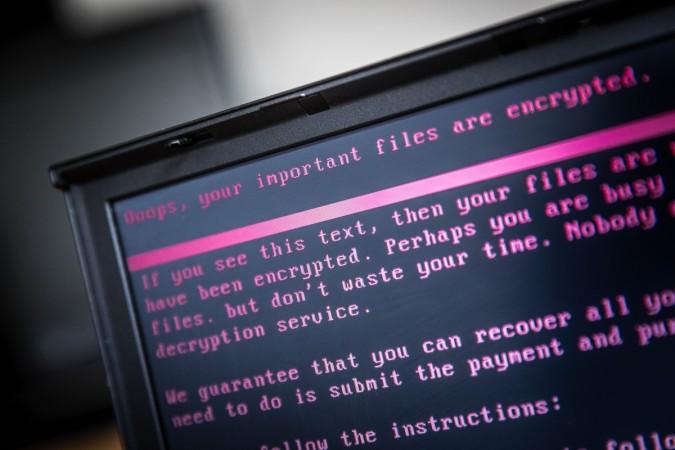
The new Petya ransomware included a message urging victims to pay $300 in Bitcoin to have their files decrypted and restored. But people, who have been infected by the ransomware, are now ended up with another pickle – they can no longer contact the attackers as the email account the virus was using to manage ransomware demands has now been blocked.
The hackers behind the Petya ransomware asked victims to send their $300 payment to a Bitcoin wallet, and then send an email with a unique identifier to wowsmith123456@posteo.net and receive the decryption keys. But, the German email provider Posteo said on its official blog post on Tuesday that it had already blocked all account access to the "wowsmith" address.
"We do not tolerate the misuse of our platform: The immediate blocking of misused email accounts is the necessary approach by providers in such cases," the company said.
While paying up the ransom never guarantees the recovery of encrypted files, the blocking of the email address now leaves little chance of getting the files back by paying the ransom.
So, the bottom line for all the victims of Petya ransomware is "don't pay the ransom."
It's still unclear if anyone managed to decrypt an infected system by paying the ransom before the email was blocked. Meanwhile, only about 20 victims have reportedly paid about $5,000 in total to the hackers.
You can still prevent encryption
Malware Tech, the cyber security blog run by the security researcher who found the WannaCry kill switch, said that Petya ransomware victims have nearly an hour after getting infected to take one final step to avoid the encryption.
If machine reboots and you see this message, power off immediately! This is the encryption process. If you do not power on, files are fine. pic.twitter.com/IqwzWdlrX6
— Hacker Fantastic (@hackerfantastic) June 27, 2017
According to the blog post, Petya starts encrypting files only after reboot. The ransomware sets an automatic reboot for an infected system after one hour, allowing victims to prevent encryption by simply shutting down the computer before it reboots.
The next step would be to try and rescue the files from the machine.
Alert level: Severe
Meanwhile, Microsoft has set a "Sever" alert level for the Petya ransomware, which, according to the company, "can stop you from using your PC or accessing your data."

Microsoft said that the ransomware infected more than 12,500 machines in Ukraine on Tuesday, before spreading to 64 countries, including Belgium, Brazil, Germany, Russia and the United States. The company also confirmed that the update system of the Ukrainian company M.E.Doc was responsible for at least some of the initial infections.
However, M.E.Doc has denied being the initial infection vector on its Facebook page.












