Popular search engine giant Yahoo has been a victim of a series of hacking for past several years, but they were reported to be of minor or negligible proportion. Now, shocking evidence has emerged that Yahoo email server hacking in 2013 was actually much bigger than it was previously disclosed by the company.
Yahoo's 2013 hacking report, which has been recently updated in the company's archive, states that more than three billion user details were compromised, not one billion as initially thought, making one of the biggest hacking incidents to date.
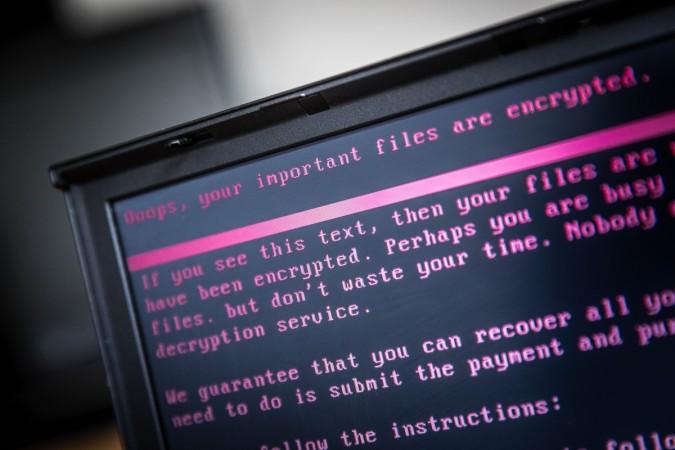
Also read- Cyber Attack Alert: nRansomware demands your nude photos to recover locked files
It has come light that Yahoo, back in 2013 had weak MD5 cryptographic hashing algorithm and the hackers broke open the firewall and possibly stole users' names, e-mail addresses, telephone numbers, dates of birth and passwords.
However, Yahoo's hired cyber forensic investigators are optimistic that the users' passwords (in clear text), payment card data, or bank account information were untouched and remained safe.
"We recently obtained additional information and, after analyzing it with the assistance of outside forensic experts, we have identified additional user accounts that were affected," Yahoo said in a press release.
"Based on an analysis of the information with the assistance of outside forensic experts, Yahoo has determined that all accounts that existed at the time of the August 2013 theft were likely affected."
With increasing cases of ransomware attacks, users and corporate companies are advised to be vigilant while opening emails from unknown senders and also ensure the PCs have best anti-virus software.
Here's how to protect your PCs from ransomware and malware:
- Always keep your PCs updated with the latest firmware; most software companies including Microsoft and Apple usually send software updates regularly in terms of weekly or monthly and make sure to update them immediately
- Make sure to use premium Anti-virus software, which also provides malware protection and Internet security
- Never open email sent from unknown senders
- Disable ActiveX content in Microsoft Office applications such as Word, Excel, etc.
- Disable Remote Desktop Connections, employ least-privileged accounts. Limit users who can log in using Remote Desktop, set an account lockout policy. Ensure proper RDP logging and configurations
- Never install plugins (for browsers) and application software on the PCs from un-familiar publishers
- System administrators in corporate companies should establish a Sender Policy Framework (SPF) for their domain, which is an email validation system designed to prevent spam by detecting email spoofing by which most of the ransomware samples successfully reaches the corporate email boxes.
Additional security measures that may be considered by system administrators:
- Use RDP Gateways for better management
- Change the listening port for Remote Desktop
- Tunnel Remote Desktop connections through IPSec or SSH
- Two-factor authentication may also be considered for highly critical systems















